You've got sensitive documents—financial reports, contracts, personal information, confidential business data. These need real protection, not just basic password protection. How do professionals actually secure their important PDFs?
Our Protect PDF tool makes implementing layered security simple. You can add strong passwords and permission restrictions in one place. Protecting sensitive documents requires a layered approach. No single method is perfect, but combining multiple security measures creates effective protection. Let me show you how professionals actually do it, and how our tool helps.
The Layered Security Approach
Real-world document protection uses multiple layers:
Layer 1: Strong passwords. Use our Protect PDF tool to add long, random passwords for PDF encryption.
Layer 2: Permission restrictions. Use our tool to limit what users can do (print, copy, edit).
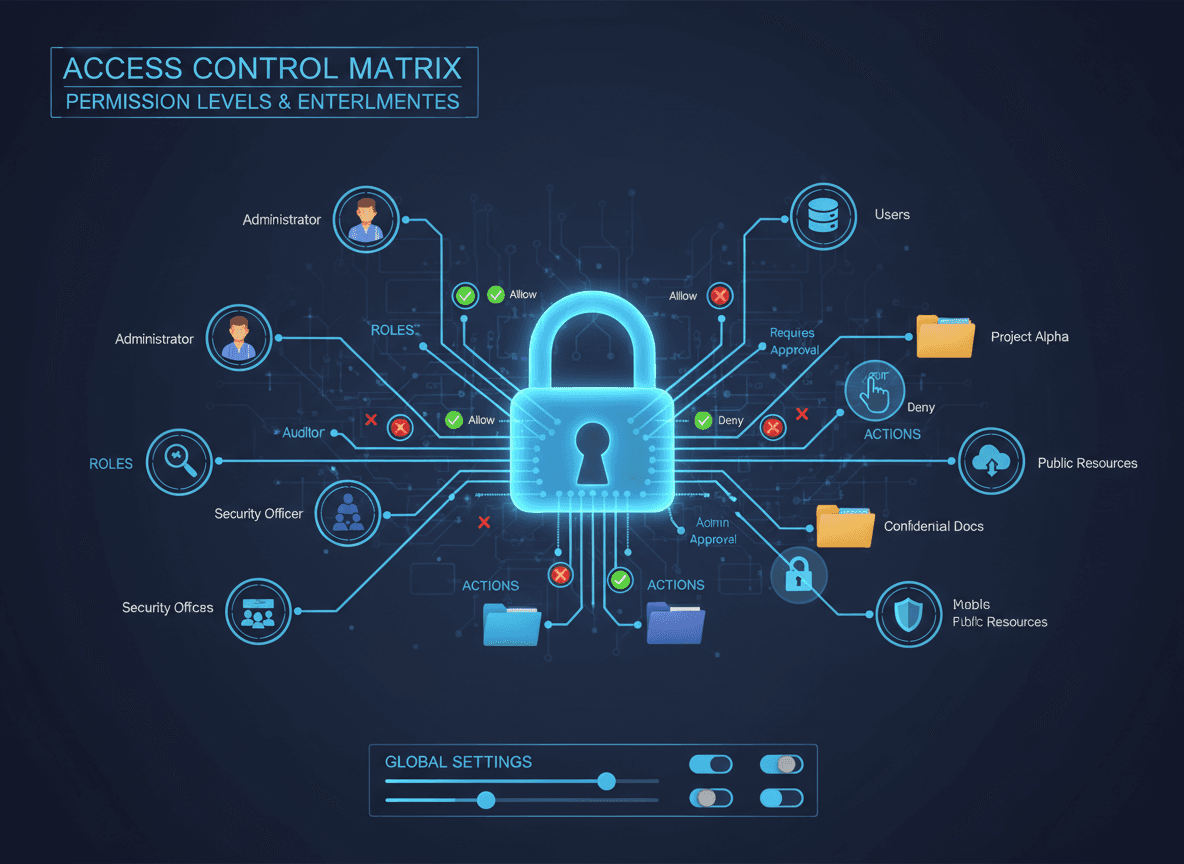
Layer 3: Access control. Control who has access to the document.
Layer 4: Secure sharing. Use secure methods to share documents.
Layer 5: Monitoring. Track who accesses documents and when.
Layer 6: Legal protection. Include terms, watermarks, or legal notices.
For Financial Documents
Financial documents need strong protection:
Strong encryption. Use 256-bit encryption with strong passwords.
Restrict printing and copying. Prevent easy duplication of financial data.
Access logging. Track who views financial documents.
Secure distribution. Use encrypted email or secure file sharing services.
Time-limited access. Consider documents that expire or require re-authentication.
Watermarks. Add watermarks with user identification for tracking.
For Legal Contracts
Contracts need protection and legal validity:
Strong passwords. Protect contracts with strong encryption.
Restrict editing. Prevent unauthorized modifications to contract terms.
Digital signatures. Use digital signatures for legal validity.
Access control. Limit access to authorized parties only.
Audit trails. Maintain records of who accessed and when.
Legal watermarks. Include legal notices or confidentiality markings.
For Personal Information
Documents with personal information need privacy protection:
Strong encryption. Encrypt documents containing personal data.
Restrict access. Only share with authorized recipients.
Secure deletion. Ensure documents are properly deleted after use.
Compliance. Follow privacy regulations (GDPR, HIPAA, etc.).
Minimal sharing. Only share what's necessary, not entire documents.
Time limits. Consider documents that expire automatically.
For Business Confidential Documents
Confidential business documents need comprehensive protection:
Multi-layer security. Combine passwords, restrictions, and access control.
User identification. Track who accesses documents.
Distribution control. Control how documents are shared.
Expiration dates. Set documents to expire or require renewal.
Watermarks. Add identifying watermarks for tracking.
Legal notices. Include confidentiality and legal notices.
Best Practices for Sensitive Documents
Here's what professionals do:
Use strong passwords. 20+ character random passwords for important documents.
Combine security measures. Don't rely on one method—use multiple layers.
Control access. Only share with people who need access.
Use secure sharing methods. Encrypted email, secure file sharing, not regular email.
Track access. Monitor who views documents when possible.
Set expiration. Consider time-limited access for sensitive documents.
Include legal protection. Watermarks, terms, and legal notices.
Test security. Try to bypass your own security to test effectiveness.
Keep backups securely. Store backups with the same security as originals.
Document security measures. Note what security you've applied.
Common Mistakes
Weak passwords. Using simple passwords defeats the purpose.
Single layer security. Relying on only one security measure.
Insecure sharing. Sending sensitive documents via unencrypted email.
No access control. Sharing with too many people or wrong people.
No monitoring. Not tracking who accesses documents.
Forgetting expiration. Not setting time limits on sensitive documents.
No backups. Not having secure backups of important documents.
Tools and Services
PDF encryption tools. Use our Protect PDF tool with strong encryption (256-bit AES).
Secure file sharing. Services with encryption and access control.
Digital signature services. For legal validity and authentication.
Access management. Tools that track and control document access.
Watermarking tools. For document identification and tracking.
Protecting Sensitive Documents Properly
I've secured hundreds of sensitive documents, and here's what I've learned: protecting sensitive documents requires a layered approach. Our Protect PDF tool helps you implement these layers easily. Strong passwords. Permission restrictions. Access control. Secure sharing. Monitoring. Legal protection. No single method is perfect, but combining multiple measures creates effective security.
For financial, legal, personal, or confidential documents, use multiple security layers with our tool. Use strong encryption through our Protect PDF tool. Control access. Share securely. Monitor usage. Take time to implement proper security—sensitive documents deserve proper protection. I've seen people rely on just a password, and that's not enough for truly sensitive content.
The key is understanding that document security is about layers. Each layer adds protection, and together they create effective security. Our Protect PDF tool makes implementing these layers simple. Don't rely on one method—use multiple measures appropriate for your document's sensitivity level. More sensitive documents need more layers.
Ready to protect your sensitive documents? Try our Protect PDF tool now and add strong password protection and permission restrictions to your PDFs.